Connect the PDC agent via Azure Private Link
Azure Private Link lets you connect PDC agents running in your Azure Virtual Network to Grafana Cloud while staying on the Azure network. This improves security and helps lower your Azure egress costs.
Before you begin
To use Azure Private Link, you need the following:
- A Grafana Cloud stack hosted on Azure. To check where your stack is hosted, navigate to your account in Grafana Cloud, and click Details for a given service, such as Prometheus or Loki. If the region matches one of the Azure regions where Grafana Cloud is hosted, then your stack is hosted on Azure.
Note
If your stack is not hosted on Azure, you must create a new stack hosted on Azure.
- An Azure Virtual Network in which to create the Private Endpoint for your PDC agent.
Other regions
Azure Private Link supports cross-regional connections. If your infrastructure is hosted in a different Azure region than the one where your Grafana Cloud stack is hosted, you can still connect your PDC agents via Private Link.
Set up Azure Private Link for PDC
Note
The Azure Private Link service used to connect PDC agents is the same as the one used to send telemetry to Grafana Cloud via Azure Private Link.
If you already have a Private Endpoint and
grafana.netPrivate DNS zone configured for sending telemetry, skip to Add PDC DNS records to add the PDC-specific DNS entries.
Setting up Azure Private Link for PDC requires two steps:
- Create a Private Endpoint and Private DNS zone.
- Add DNS records for the PDC endpoints.
After setup is complete, you can connect the PDC agent using the standard configuration.
Create a Private Endpoint
Create a Private Endpoint in the Azure console, or provision one using Terraform.
Use the Azure Console
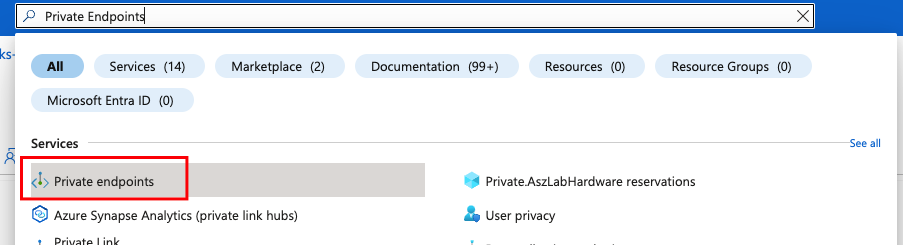
Open your Azure Console and navigate to Private Endpoints.
![Select Private Endpoint > Endpoints]()
Choose Create.
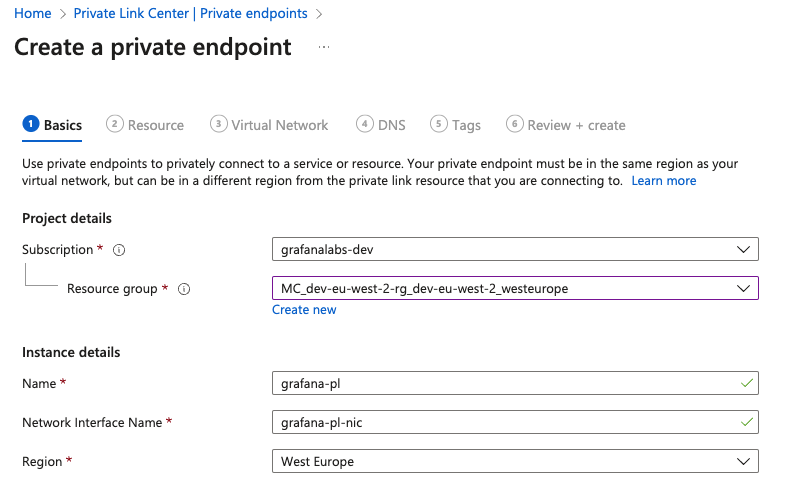
Select the subscription and resource group where your virtual network is.
Give the endpoint a name, for example,
grafana-pl.![Enter name]()
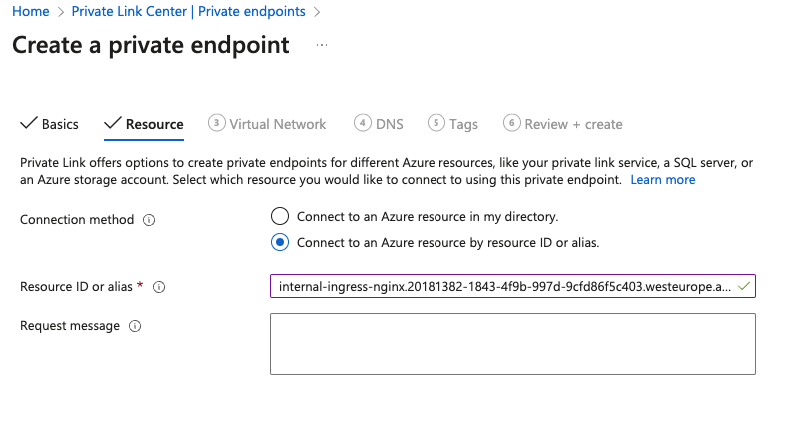
Continue to the Resource tab and select Connect to an Azure resource by resource ID or alias.
In the Resource ID or alias field, enter the service alias for your Grafana Cloud stack region.
![Select service]()
In the Request Message field, add some text for future reference, like your Grafana organization name.
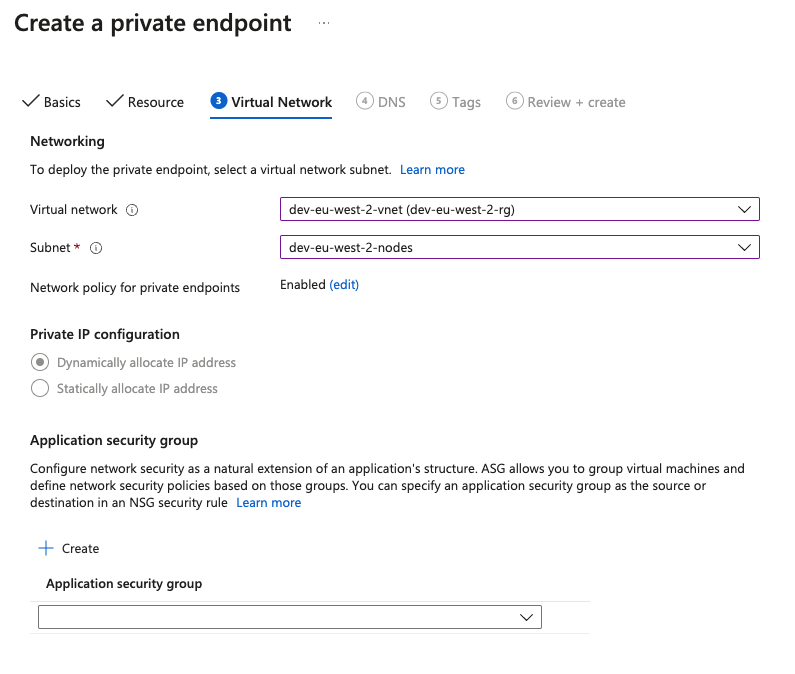
Continue to Virtual Network. Select your Virtual Network and Subnet.
![Network]()
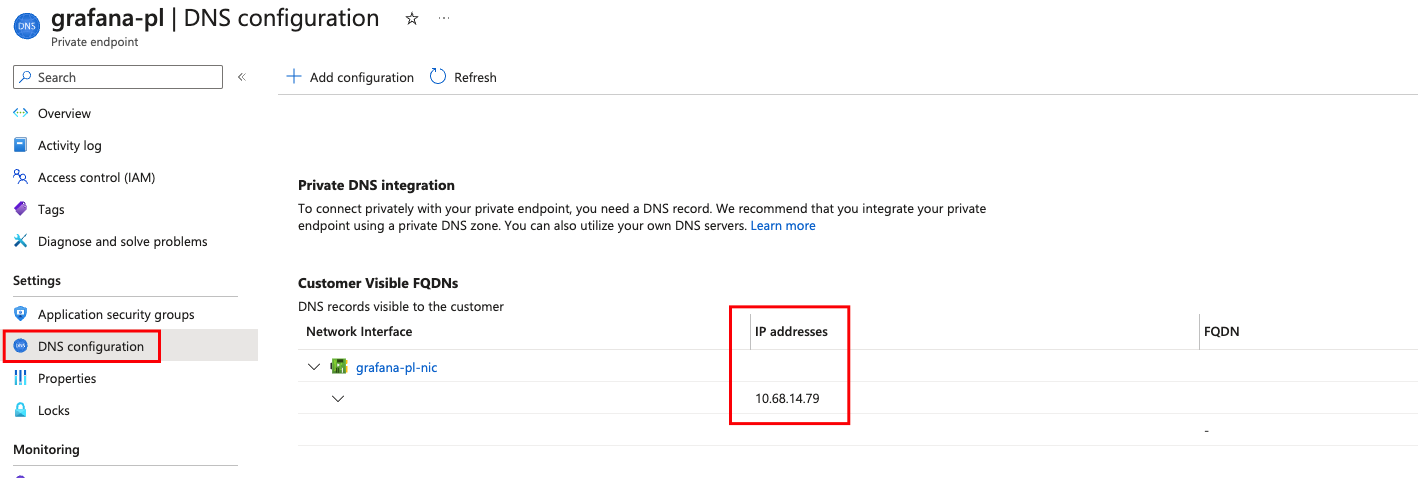
Choose Review + Create and proceed to create the resource. The Private Endpoint is created with
Awaiting Approvalstatus. After a maximum of 10 minutes, the connection is automatically approved and the status transitions toApproved. If the status stays asAwaiting Approval, contact Grafana Support to request the manual approval of the connection.Under DNS Configuration, copy the local IP address of the private endpoint. You need this IP for the DNS records in the next steps.
![IP Address]()
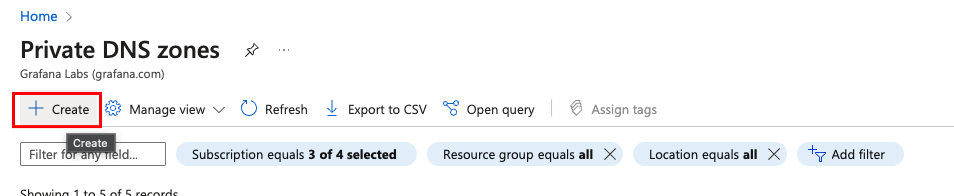
Navigate to Private DNS zones and click on Create.
![Create DNS Zone]()
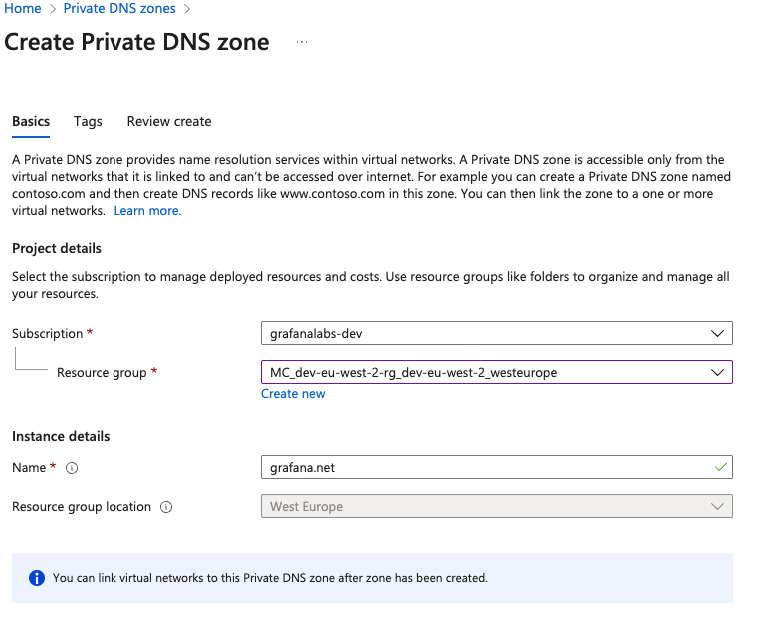
Select the subscription and resource group.
In Instance Details > Name, enter
grafana.netand then proceed to create.![DNS Zone]()
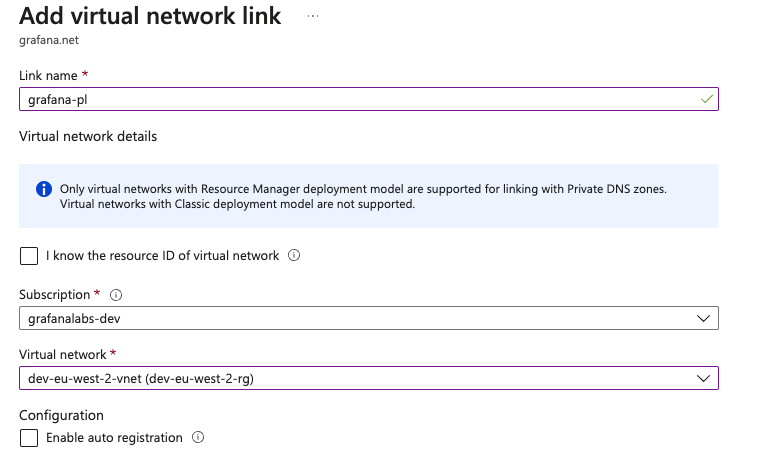
Navigate to Virtual network links, then click on Add.
Name the network link, for example
grafana-pl.Select your subscription and Virtual Network.
![Virtual Network Link]()
Use Terraform
Use the following snippet to automate Private Endpoint setup in Azure using Terraform:
locals {
region = "<your azure region>"
resource_group_name = "<your resource group name>"
vnet_id = "<your virtual network id>"
subnet_id = "<your subnet id>"
privatelink_service_alias = "<private link service alias provided by Grafana>"
}
resource "azurerm_private_endpoint" "privatelink_grafana" {
name = "grafana-pl"
location = local.region
resource_group_name = local.resource_group_name
subnet_id = local.subnet_id
private_service_connection {
name = "grafana-pl"
is_manual_connection = true
request_message = "connection request from <customer grafana org name>"
private_connection_resource_alias = local.privatelink_service_alias
}
}
resource "azurerm_private_dns_zone" "privatelink_grafana" {
name = "grafana.net"
resource_group_name = local.resource_group_name
}
resource "azurerm_private_dns_zone_virtual_network_link" "privatelink_grafana" {
name = "grafana-pl"
resource_group_name = local.resource_group_name
private_dns_zone_name = azurerm_private_dns_zone.privatelink_grafana.name
virtual_network_id = local.vnet_id
}Add PDC DNS records
After the Private Endpoint and grafana.net Private DNS zone are configured, add DNS A records for the two PDC endpoints. These records ensure that the PDC agent resolves Grafana Cloud hostnames to the Private Endpoint IP, routing traffic through Azure Private Link instead of the public internet.
The PDC agent connects to two endpoints:
- API endpoint:
private-datasource-connect-api-<cluster>.grafana.net(port 443) — used for signing short-lived SSH certificates. - SSH endpoint:
private-datasource-connect-<cluster>.grafana.net(port 22) — used for the SSH tunnel that carries data source queries.
Replace <cluster> with the cluster value for your stack, which is displayed in the Grafana UI under Connections > Private data source connections > Configuration Details.
Use the Azure Console
- Navigate to your
grafana.netPrivate DNS zone. - Click Record set to add a new record.
- In Name, enter
private-datasource-connect-api-<cluster>(replacing<cluster>with your cluster value). - In IP Address, enter the local IP address of the Private Endpoint.
- Click OK to create the record.
- Repeat the previous steps for the SSH endpoint, using
private-datasource-connect-<cluster>as the Name.
Use Terraform
Add the following resources to the Terraform configuration from the previous step, and add pdc_cluster to the existing locals block:
locals {
# Add to existing locals block
pdc_cluster = "<your PDC cluster value>"
}
resource "azurerm_private_dns_a_record" "privatelink_grafana_pdc_api" {
name = "private-datasource-connect-api-${local.pdc_cluster}"
zone_name = azurerm_private_dns_zone.privatelink_grafana.name
resource_group_name = local.resource_group_name
ttl = 300
records = [azurerm_private_endpoint.privatelink_grafana.private_service_connection[0].private_ip_address]
}
resource "azurerm_private_dns_a_record" "privatelink_grafana_pdc_ssh" {
name = "private-datasource-connect-${local.pdc_cluster}"
zone_name = azurerm_private_dns_zone.privatelink_grafana.name
resource_group_name = local.resource_group_name
ttl = 300
records = [azurerm_private_endpoint.privatelink_grafana.private_service_connection[0].private_ip_address]
}Connect the PDC agent
Once the Private Endpoint and PDC DNS records are in place, the PDC agent automatically routes traffic through Azure Private Link. No special agent flags are needed because DNS resolution handles the routing.
Run the PDC agent using the standard configuration. For instructions on deploying the PDC agent, refer to Configure private data source connect (PDC).
To verify that your PDC agent successfully connected to Grafana Cloud, check the agent logs for the following message:
This is Grafana Private Data Source Connect!