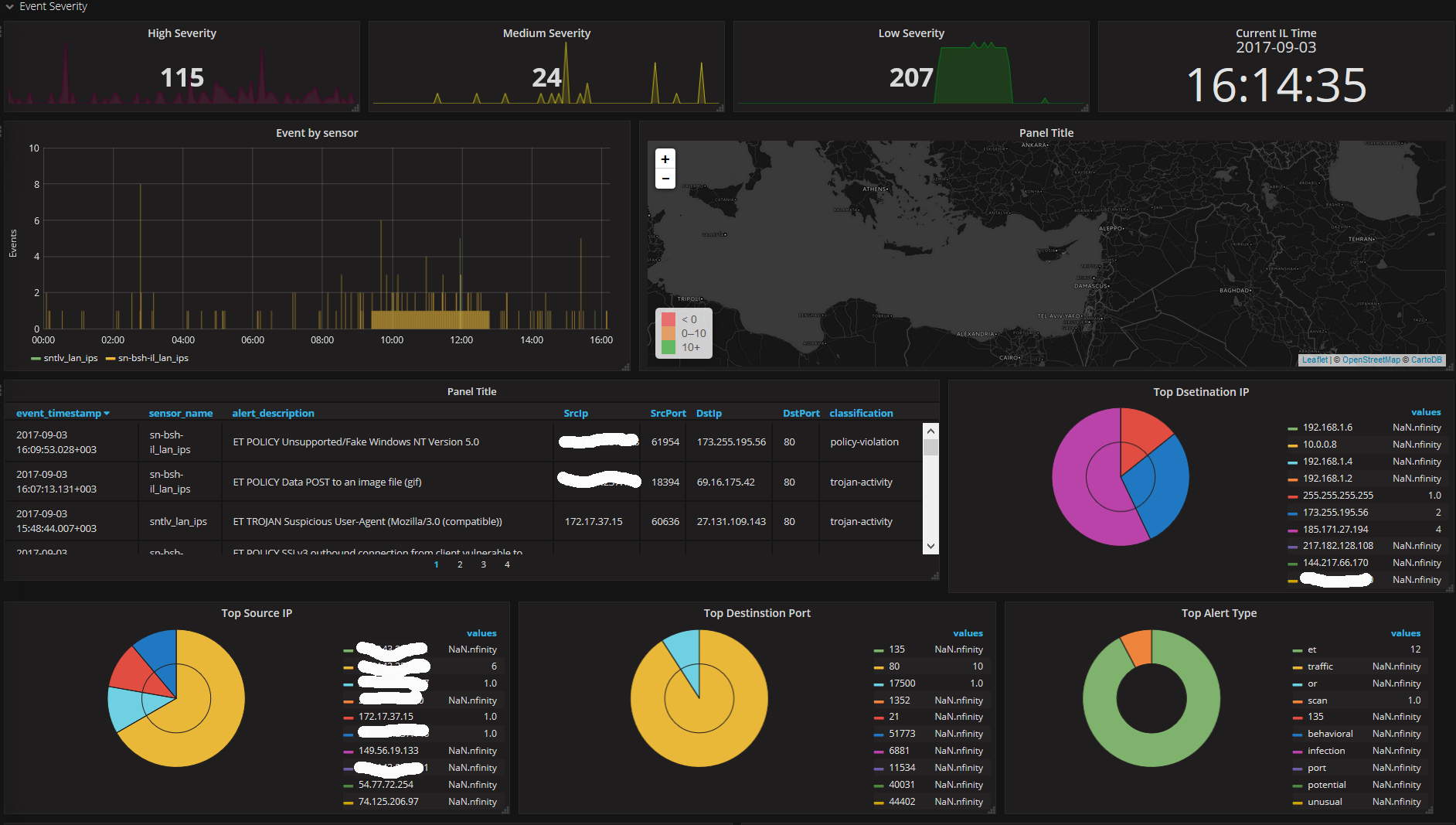
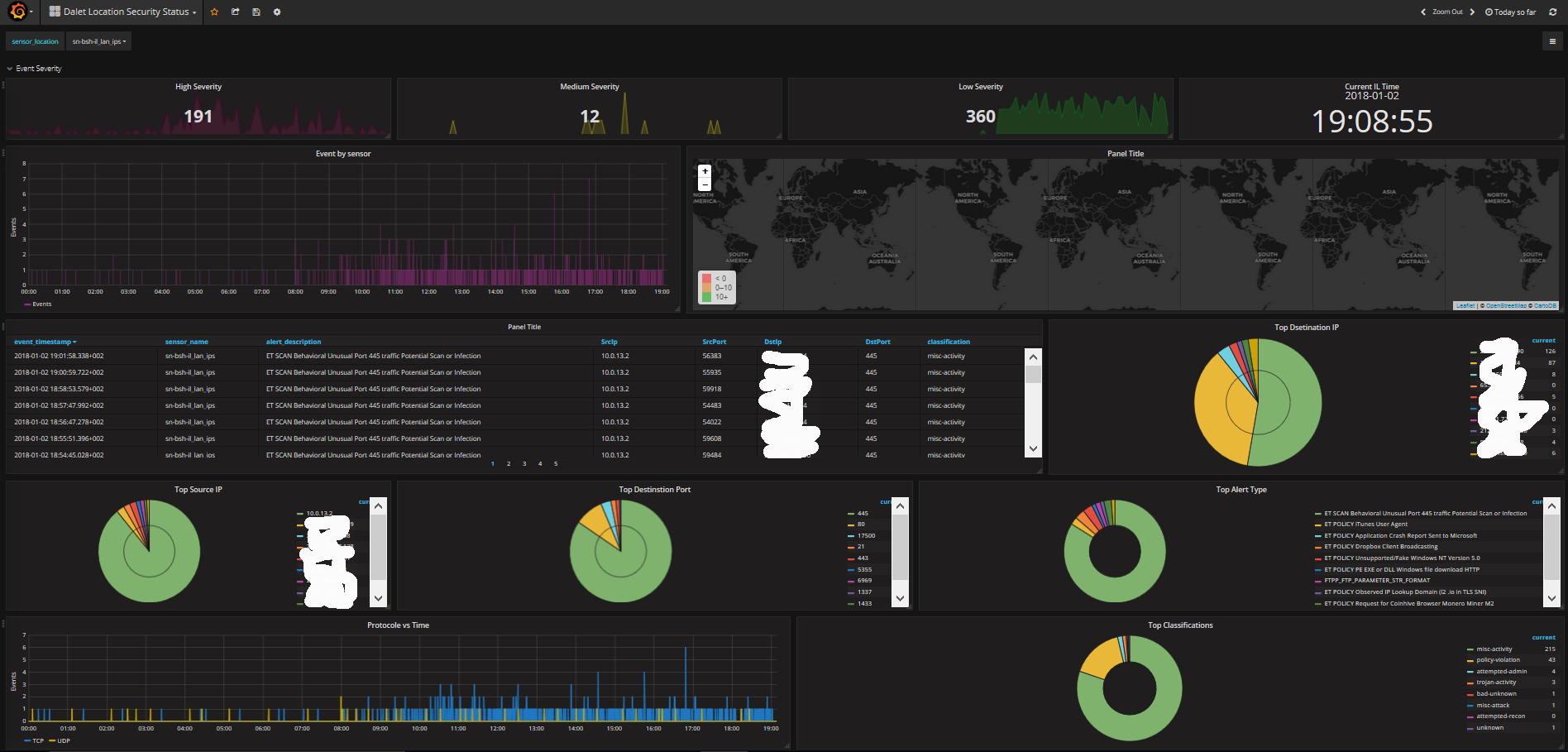
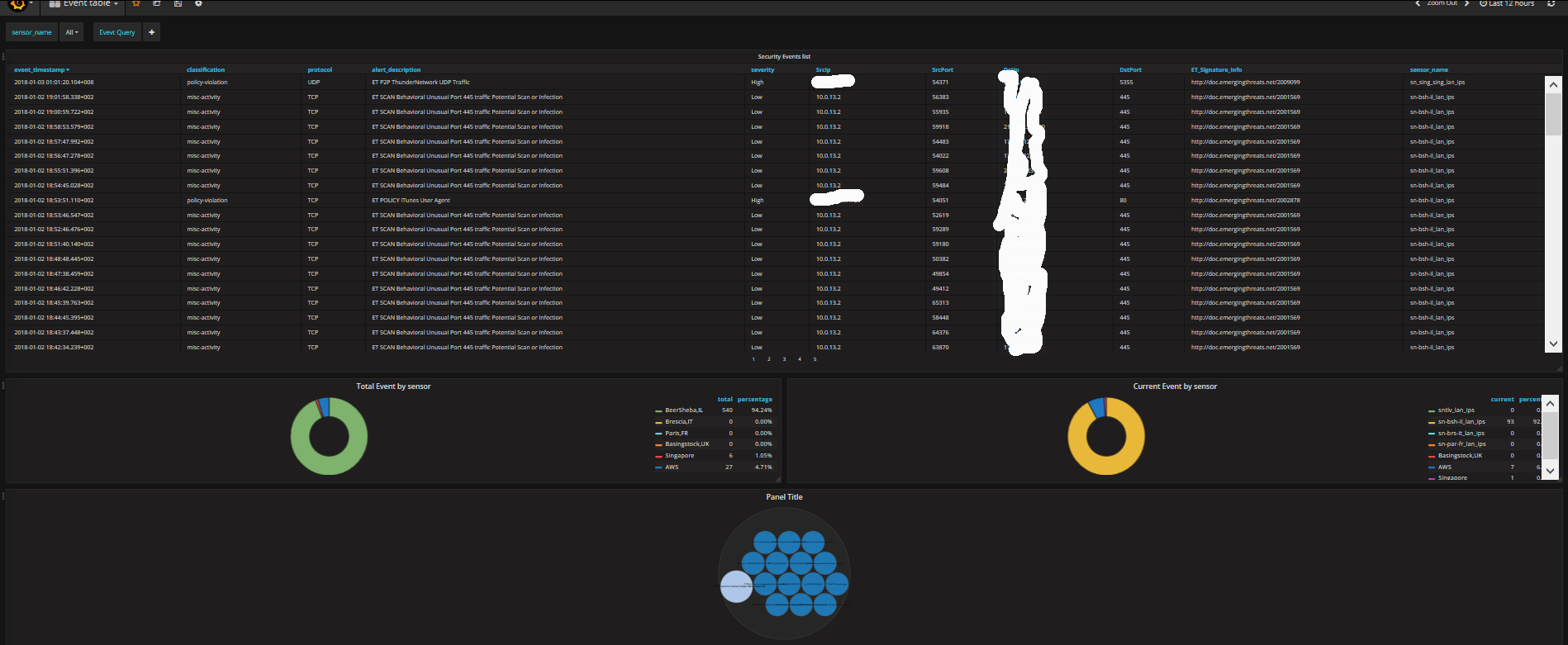
Security center
Security feed from Pfsense snort Barnyard2 output
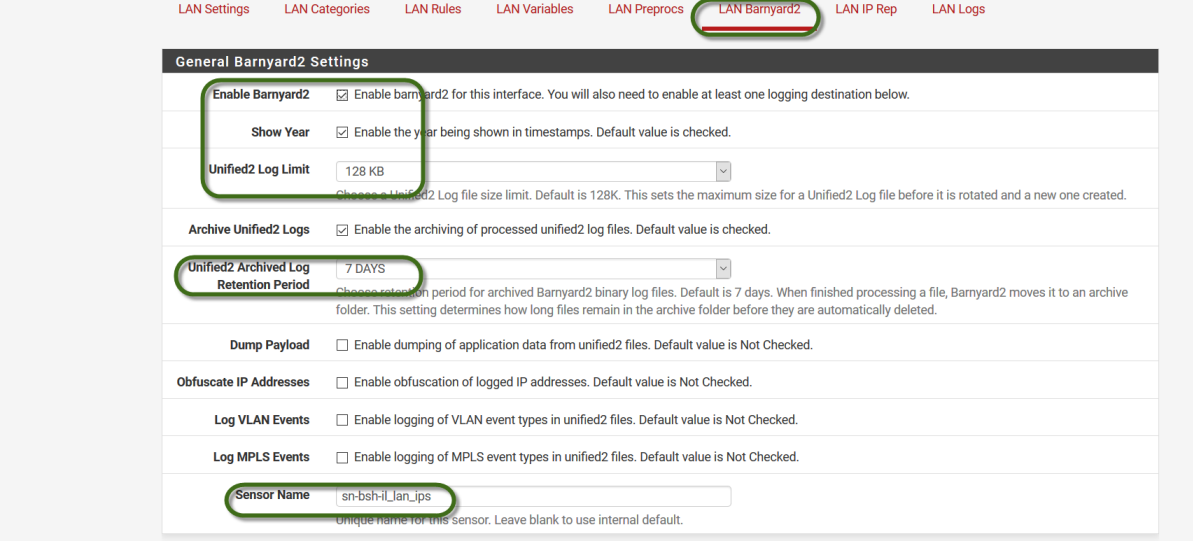
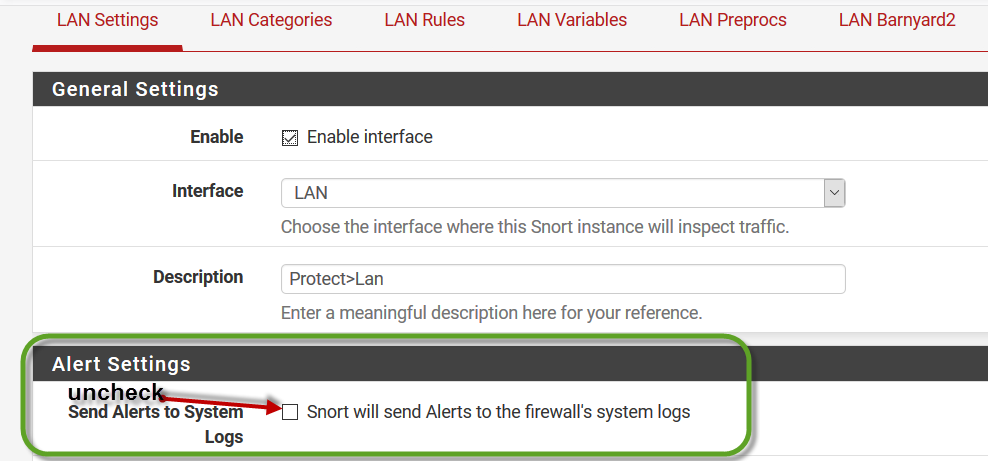
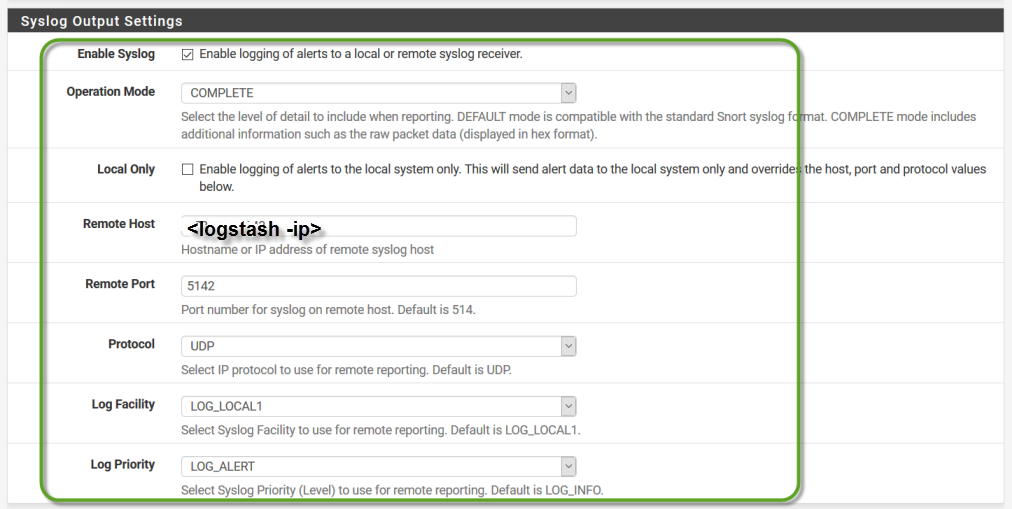
Using Logstash receiver and Elasticsearch , Snort add-on on Pfsenese Firewall and Barnyard2 sends syslogs sends to Logstasth act as syslog listener and store into elasticsearch Added few screenshot for configuratiuon tips , and in addition my Logstash input file config
Logstash config file
Author: Tal Bar-Or
Email: tbaror@dalet.com
Last Update: 11/18/2016
This conf file is based on accepting logs for snort
input { udp { port => 5142 type => snort } } filter { if [host] =~ /172.17.37.2/ or [host] =~ /10.0.8.2/ or [host] =~ /10.0.11.2/ or [host] =~ /10.0.10.2/ or [host] =~ /10.0.12.2/ or [host] =~ /10.0.14.2/ or [host] =~ /10.0.15.2/{ # This is the initial parsing of the log grok { match => { "message" => "|%{SPACE}[%{WORD:msg_source}[%{WORD:msg}]:%{SPACE}[%{GREEDYDATA:sensor_name}]%{SPACE}]%{SPACE}||%{SPACE}%{TIMESTAMP_ISO8601:event_timestamp}%{SPACE}%{INT:event_priority}%{SPACE}[%{INT:gid}:%{INT:sid}:%{INT:rev}]%{SPACE}%{DATA:alert_description}||%{SPACE}%{DATA:classification}%{SPACE}||%{SPACE}%{INT:protocol}%{SPACE}%{IP:SrcIp}%{SPACE}%{IP:DstIp}%{SPACE}||%{SPACE}%{INT:SrcPort}%{SPACE}%{INT:DstPort}%{SPACE}"} } # If you'd like to collect the DNS name for the SrcIP keep this section. Caution, this can cause an attacker to go into hiding. # If you do not want reverse DNS lookups of IPs keep this uncommented. #mutate { # add_field => { "SrcIP-resolved" => "%{SrcIp}" } #} #dns { # reverse => [ "[SrcIP-resolved]" ] # action => "replace" #}
# This will attempt to do a geoip lookup against the SrcIP
geoip {
source => "SrcIp"
target => "SrcGeoip"
database => "/etc/logstash/GeoLite2-City.mmdb"
add_field => [ "[SrcGeoip][coordinates]", "%{[geoip][longitude]}" ]
add_field => [ "[SrcGeoip][coordinates]", "%{[geoip][latitude]}" ]
}
mutate {
convert => [ "[SrcGeoip][coordinates]", "float"]
}
#geoip {
# source => "[SrcIp]"
# target => "SrcGeo"
#}
If you'd like to collect the DNS name for the DstIP keep this section. Caution, this can cause an attacker to go into hiding.
If you do not want reverse DNS lookups of IPs keep this uncommented.
#mutate {
add_field => { "DstIP-resolved" => "%{DstIp}" }
#}
#dns {
reverse => [ "[DstIP-resolved]" ]
action => "replace"
#}
This will attempt to do a geoip lookup against the DstIP
geoip {
source => "DstIp"
target => "DstGeoip"
database => "/etc/logstash/GeoLite2-City.mmdb"
add_field => [ "[DstGeoip][coordinates]", "%{[geoip][longitude]}" ]
add_field => [ "[DstGeoip][coordinates]", "%{[geoip][latitude]}" ]
}
mutate {
convert => [ "[DstGeoip][coordinates]", "float"]
}
#geoip {
source => "[DstIp]"
target => "DstGeo"
#}
If the alert is a Snort GPL alert break it apart for easier reading and categorization
if [alert_description] =~ "GPL " {
This will parse out the category type from the alert
grok {
match => { "alert" => "GPL\s+%{DATA:category}\s" }
}
This will store the category
mutate {
add_field => { "rule_type" => "Snort GPL" }
lowercase => [ "category"]
}
}
If the alert is an Emerging Threat alert break it apart for easier reading and categorization
if [alert_description] =~ "ET " {
This will parse out the category type from the alert
grok {
match => { "alert" => "ET\s+%{DATA:category}\s" }
}
This will store the category
mutate {
add_field => { "rule_type" => "Emerging Threats" }
lowercase => [ "category"]
}
}
I recommend changing the field types below to integer so searches can do greater than or less than
and also so math functions can be ran against them
mutate {
convert => [ "SrcPort", "integer" ]
convert => [ "DstPort", "integer" ]
convert => [ "event_priority", "integer" ]
convert => [ "protocol", "integer" ]
remove_field => [ "message"]
}
This will translate the priority field into a severity field of either High, Medium, or Low
if [event_priority] == 1 {
mutate {
add_field => { "severity" => "High" }
}
}
if [event_priority] == 2 {
mutate {
add_field => { "severity" => "Medium" }
}
}
if [event_priority] == 3 {
mutate {
add_field => { "severity" => "Low" }
}
}
This section adds URLs to lookup information about a rule online
mutate {
add_field => [ "ET_Signature_Info", "http://doc.emergingthreats.net/%{sid}" ]
add_field => [ "Snort_Signature_Info", "https://www.snort.org/search?query=%{gid}-%{sid}" ]
}
#protocol type detection
if [protocol] == 17 {
mutate {
replace => { "protocol" => "UDP" }
}
}
if [protocol] == 6 {
mutate {
replace => { "protocol" => "TCP" }
}
}
if [protocol] == 1 {
mutate {
replace => { "protocol" => "ICMP" }
}
}
if [protocol] == 2 {
mutate {
replace => { "protocol" => "IGMP" }
}
}
} }
output { if [msg_source]== "SNORTIDS" { elasticsearch { index => "ids_sensors" hosts => ["localhost:9200"]} stdout { codec => rubydebug }
} }
Data source config
Collector config:
Upload an updated version of an exported dashboard.json file from Grafana
| Revision | Description | Created | |
|---|---|---|---|
| Download |