Microsoft SQL Server integration for Grafana Cloud
Microsoft SQL Server is a relational database that can be used to store and retrieve data. The Microsoft SQL Server integration uses Grafana Alloy to collect metrics for monitoring a MSSQL instance, including aspects such as active connections, read/write latency, buffer cache hit rate, and page faults. Accompanying dashboards are provided to visualize these metrics, as well as recommended alerting policies.
This integration supports SQL Server 2017, SQL Server 2019, and SQL Server 2022.
This integration includes 5 useful alerts and 3 pre-built dashboards to help monitor and visualize Microsoft SQL Server metrics and logs.
Before you begin
In order to scrape Microsoft SQL Server metrics, you must have a user configured with the following grants:
GRANT VIEW ANY DEFINITION TO <MONITOR_USER>;
GRANT VIEW SERVER STATE TO <MONITOR_USER>;Install Microsoft SQL Server integration for Grafana Cloud
- In your Grafana Cloud stack, click Connections in the left-hand menu.
- Find Microsoft SQL Server and click its tile to open the integration.
- Review the prerequisites in the Configuration Details tab and set up Grafana Alloy to send Microsoft SQL Server metrics and logs to your Grafana Cloud instance.
- Click Install to add this integration’s pre-built dashboards and alerts to your Grafana Cloud instance, and you can start monitoring your Microsoft SQL Server setup.
Configuration snippets for Grafana Alloy
Simple mode
These snippets are configured to scrape a single Microsoft SQL Server instance running locally with default ports.
First, manually copy and append the following snippets into your alloy configuration file.
Integrations snippets
prometheus.exporter.mssql "integrations_mssql" {
connection_string = "sqlserver://user:pass@127.0.0.1:1433"
}
discovery.relabel "integrations_mssql" {
targets = prometheus.exporter.mssql.integrations_mssql.targets
rule {
target_label = "instance"
replacement = constants.hostname
}
rule {
target_label = "job"
replacement = "integrations/mssql"
}
}
prometheus.scrape "integrations_mssql" {
targets = discovery.relabel.integrations_mssql.output
forward_to = [prometheus.remote_write.metrics_service.receiver]
job_name = "integrations/mssql"
}Logs snippets
linux
local.file_match "logs_integrations_integrations_mssql_linux" {
path_targets = [{
__address__ = "localhost",
__path__ = "/var/opt/mssql/log/errorlog",
}]
}
loki.process "logs_integrations_integrations_mssql_linux" {
forward_to = [loki.write.grafana_cloud_loki.receiver]
stage.multiline {
firstline = "^\\s*\\d{4}-\\d{2}-\\d{2}\\s+\\d{2}:\\d{2}:\\d{2}\\.\\d+"
max_lines = 0
max_wait_time = "3s"
}
stage.regex {
expression = "^(?s)(?P<timestamp>\\s*\\d{4}-\\d{2}-\\d{2}\\s+\\d{2}:\\d{2}:\\d{2}\\.\\d+)\\s+(?P<component>\\w+)\\s+(?P<message>.*)$"
}
stage.timestamp {
source = "timestamp"
format = "RFC3339Nano"
}
stage.static_labels {
values = {
instance = constants.hostname,
job = "integrations/mssql",
log_type = "mssql_error",
}
}
stage.labels {
values = {
component = null,
message = null,
}
}
}
loki.source.file "logs_integrations_integrations_mssql_linux" {
targets = local.file_match.logs_integrations_integrations_mssql_linux.targets
forward_to = [loki.process.logs_integrations_integrations_mssql_linux.receiver]
}windows
local.file_match "logs_integrations_integrations_mssql_windows" {
path_targets = [{
__address__ = "localhost",
__path__ = "/Program Files/Microsoft SQL Server/**/MSSQL/LOG/ERRORLOG",
}]
}
loki.process "logs_integrations_integrations_mssql_windows" {
forward_to = [loki.write.grafana_cloud_loki.receiver]
stage.multiline {
firstline = "^\\s*\\d{4}-\\d{2}-\\d{2}\\s+\\d{2}:\\d{2}:\\d{2}\\.\\d+"
max_lines = 0
max_wait_time = "3s"
}
stage.regex {
expression = "^(?s)(?P<timestamp>\\s*\\d{4}-\\d{2}-\\d{2}\\s+\\d{2}:\\d{2}:\\d{2}\\.\\d+)\\s+(?P<component>\\w+)\\s+(?P<message>.*)$"
}
stage.timestamp {
source = "timestamp"
format = "RFC3339Nano"
}
stage.static_labels {
values = {
instance = constants.hostname,
job = "integrations/mssql",
log_type = "mssql_error",
}
}
stage.labels {
values = {
component = null,
message = null,
}
}
}
loki.source.file "logs_integrations_integrations_mssql_windows" {
targets = local.file_match.logs_integrations_integrations_mssql_windows.targets
forward_to = [loki.process.logs_integrations_integrations_mssql_windows.receiver]
}Advanced mode
The following snippets provide examples to guide you through the configuration process.
To instruct Grafana Alloy to scrape your Microsoft SQL Server instances, manually copy and append the snippets to your alloy configuration file, then follow subsequent instructions.
Advanced integrations snippets
prometheus.exporter.mssql "integrations_mssql" {
connection_string = "sqlserver://user:pass@127.0.0.1:1433"
}
discovery.relabel "integrations_mssql" {
targets = prometheus.exporter.mssql.integrations_mssql.targets
rule {
target_label = "instance"
replacement = constants.hostname
}
rule {
target_label = "job"
replacement = "integrations/mssql"
}
}
prometheus.scrape "integrations_mssql" {
targets = discovery.relabel.integrations_mssql.output
forward_to = [prometheus.remote_write.metrics_service.receiver]
job_name = "integrations/mssql"
}This integrations uses the prometheus.exporter.mssql component to generate metrics from a Microsoft SQL Server instance.
In the Alloy configuration file a connection string with the username, password, and a host:port pair must be provided.
Also, rather than using SQL Server credentials to authenticate, it is possible to use Windows credentials by modifying the connecton_string accordingly (see the Authentication section of the Alloy MSSQL Prometheus component documentation).
The ability to pull in custom metrics (outside of the defaults) is also available for this integration. To do this, use the query_config parameter, under the integrations.mssql section of your configuration. After configuring to collect custom metrics, the default dashboards will have to be manually modified to include any reference to these new metrics.
For the full array of configuration options, refer to the prometheus.exporter.mssql component reference documentation.
This exporter must be linked with a discovery.relabel component to apply the necessary relabelings.
For each Microsoft SQL Server instance to be monitored you must create a pair of these components.
Configure the following properties within each discovery.relabel component:
instancelabel:constants.hostnamesets theinstancelabel to your Grafana Alloy server hostname. If that is not suitable, change it to a value uniquely identifies this Microsoft SQL Server instance. Make sure this label value is the same for all telemetry data collected for this instance.
You can then scrape them by including each discovery.relabel under targets within the prometheus.scrape component.
Advanced logs snippets
linux
local.file_match "logs_integrations_integrations_mssql_linux" {
path_targets = [{
__address__ = "localhost",
__path__ = "/var/opt/mssql/log/errorlog",
}]
}
loki.process "logs_integrations_integrations_mssql_linux" {
forward_to = [loki.write.grafana_cloud_loki.receiver]
stage.multiline {
firstline = "^\\s*\\d{4}-\\d{2}-\\d{2}\\s+\\d{2}:\\d{2}:\\d{2}\\.\\d+"
max_lines = 0
max_wait_time = "3s"
}
stage.regex {
expression = "^(?s)(?P<timestamp>\\s*\\d{4}-\\d{2}-\\d{2}\\s+\\d{2}:\\d{2}:\\d{2}\\.\\d+)\\s+(?P<component>\\w+)\\s+(?P<message>.*)$"
}
stage.timestamp {
source = "timestamp"
format = "RFC3339Nano"
}
stage.static_labels {
values = {
instance = constants.hostname,
job = "integrations/mssql",
log_type = "mssql_error",
}
}
stage.labels {
values = {
component = null,
message = null,
}
}
}
loki.source.file "logs_integrations_integrations_mssql_linux" {
targets = local.file_match.logs_integrations_integrations_mssql_linux.targets
forward_to = [loki.process.logs_integrations_integrations_mssql_linux.receiver]
}To monitor your Microsoft SQL Server instance logs, you will use a combination of the following components:
local.file_match defines where to find the log file to be scraped. Change the following properties according to your environment:
__address__: The Microsoft SQL Server instance address__path__: The path to the log file.instancelabel:constants.hostnamesets theinstancelabel to your Grafana Alloy server hostname. If that is not suitable, change it to a value uniquely identifies this Microsoft SQL Server instance. Make sure this label value is the same for all telemetry data collected for this instance.
loki.process defines how to process logs before sending it to Loki.
loki.source.file sends logs to Loki.
windows
local.file_match "logs_integrations_integrations_mssql_windows" {
path_targets = [{
__address__ = "localhost",
__path__ = "/Program Files/Microsoft SQL Server/**/MSSQL/LOG/ERRORLOG",
}]
}
loki.process "logs_integrations_integrations_mssql_windows" {
forward_to = [loki.write.grafana_cloud_loki.receiver]
stage.multiline {
firstline = "^\\s*\\d{4}-\\d{2}-\\d{2}\\s+\\d{2}:\\d{2}:\\d{2}\\.\\d+"
max_lines = 0
max_wait_time = "3s"
}
stage.regex {
expression = "^(?s)(?P<timestamp>\\s*\\d{4}-\\d{2}-\\d{2}\\s+\\d{2}:\\d{2}:\\d{2}\\.\\d+)\\s+(?P<component>\\w+)\\s+(?P<message>.*)$"
}
stage.timestamp {
source = "timestamp"
format = "RFC3339Nano"
}
stage.static_labels {
values = {
instance = constants.hostname,
job = "integrations/mssql",
log_type = "mssql_error",
}
}
stage.labels {
values = {
component = null,
message = null,
}
}
}
loki.source.file "logs_integrations_integrations_mssql_windows" {
targets = local.file_match.logs_integrations_integrations_mssql_windows.targets
forward_to = [loki.process.logs_integrations_integrations_mssql_windows.receiver]
}To monitor your Microsoft SQL Server instance logs, you will use a combination of the following components:
local.file_match defines where to find the log file to be scraped. Change the following properties according to your environment:
__address__: The Microsoft SQL Server instance address__path__: The path to the log file.instancelabel:constants.hostnamesets theinstancelabel to your Grafana Alloy server hostname. If that is not suitable, change it to a value uniquely identifies this Microsoft SQL Server instance. Make sure this label value is the same for all telemetry data collected for this instance.
loki.process defines how to process logs before sending it to Loki.
loki.source.file sends logs to Loki.
Kubernetes instructions
Before you begin with Kubernetes
Please note: These instructions assume the use of the Kubernetes Monitoring Helm chart
In order to scrape Microsoft SQL Server metrics, you must have a user configured with the following grants:
GRANT VIEW ANY DEFINITION TO <MONITOR_USER>;
GRANT VIEW SERVER STATE TO <MONITOR_USER>;Configuration snippets for Kubernetes Helm chart
The following snippets provide examples to guide you through the configuration process.
To scrape your Microsoft SQL Server instances, manually modify your Kubernetes Monitoring Helm chart with these configuration snippets.
Replace any values between the angle brackets <> in the provided snippets with your desired configuration values.
Metrics snippets
alloy-metrics:
extraConfig: |-
prometheus.exporter.mssql "integrations_mssql" {
connection_string = "sqlserver://<db_user>:<db_password>@<mssql_service>.<mssql_namespace>.svc.cluster.local:1433"
}
prometheus.scrape "integrations_mssql" {
targets = prometheus.exporter.mssql.integrations_mssql.targets
forward_to = [prometheus.remote_write.grafana_cloud_metrics.receiver]
job_name = "integrations/mssql"
}Logs snippets
podLogs:
extraDiscoveryRules: |-
rule {
source_labels = ["__meta_kubernetes_namespace", "__meta_kubernetes_pod_name"]
separator = ":"
regex = "(<mssql_namespace>:<mssql_pod_prefix>.*)"
replacement = "mssql"
target_label = "integration"
}
rule {
source_labels = ["integration", "__meta_kubernetes_pod_node_name"]
separator = ":"
regex = "mssql:(.*)"
target_label = "host"
}
extraLogProcessingStages: |-
stage.match {
selector = "{integration=\\"mssql\\"}"
stage.multiline {
firstline = "^\\\\s*\\\\d{4}-\\\\d{2}-\\\\d{2}\\\\s+\\\\d{2}:\\\\d{2}:\\\\d{2}\\\\.\\\\d+"
}
stage.regex {
expression = "^(?s)(?P<timestamp>\\\\s*\\\\d{4}-\\\\d{2}-\\\\d{2}\\\\s+\\\\d{2}:\\\\d{2}:\\\\d{2}\\\\.\\\\d+)\\\\s+(?P<component>\\\\w+)\\\\s+(?P<message>.*)$"
}
stage.timestamp {
format = "RFC3339Nano"
source = "timestamp"
}
stage.static_labels {
values = {
log_type = "mssql_error",
job = "integrations/mssql",
instance = "<mssql_service>.<mssql_namespace>.svc.cluster.local:1433",
}
}
stage.labels {
values = {
message = "message",
component = "component",
}
}
}Dashboards
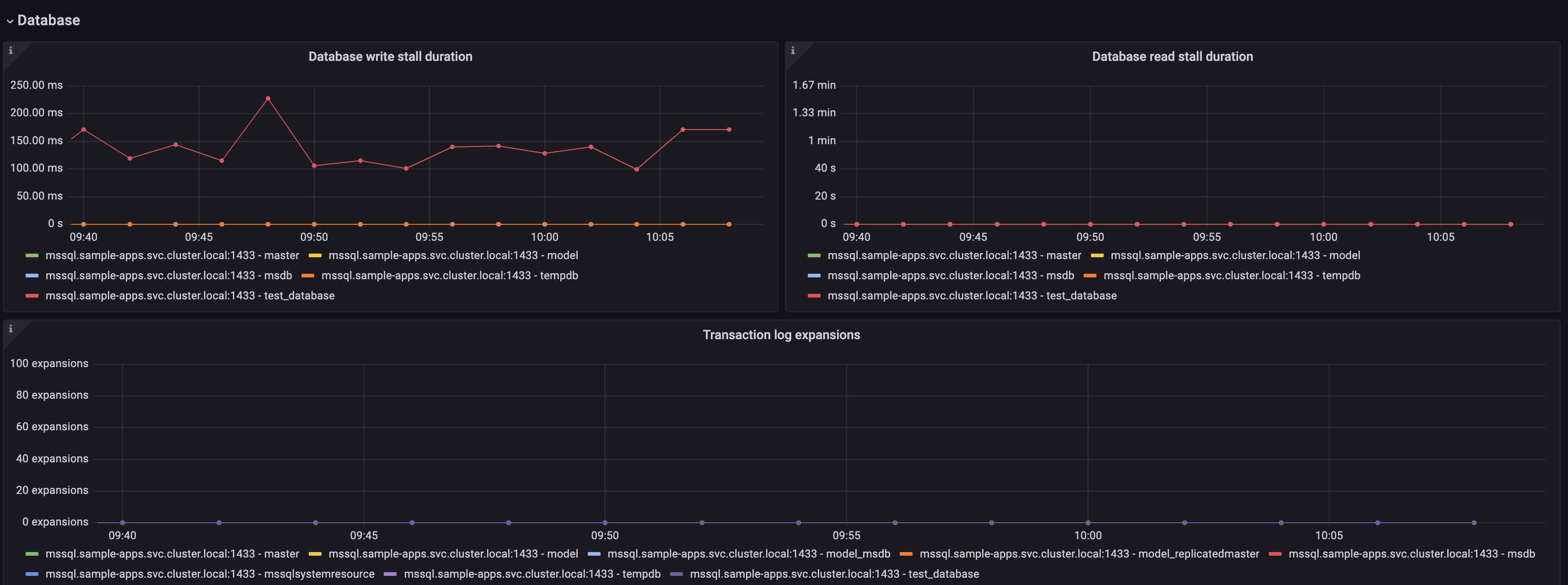
The Microsoft SQL Server integration installs the following dashboards in your Grafana Cloud instance to help monitor your system.
- MSSQL logs
- MSSQL overview
- MSSQL pages
Microsoft SQL Server overview dashboard (1/3).
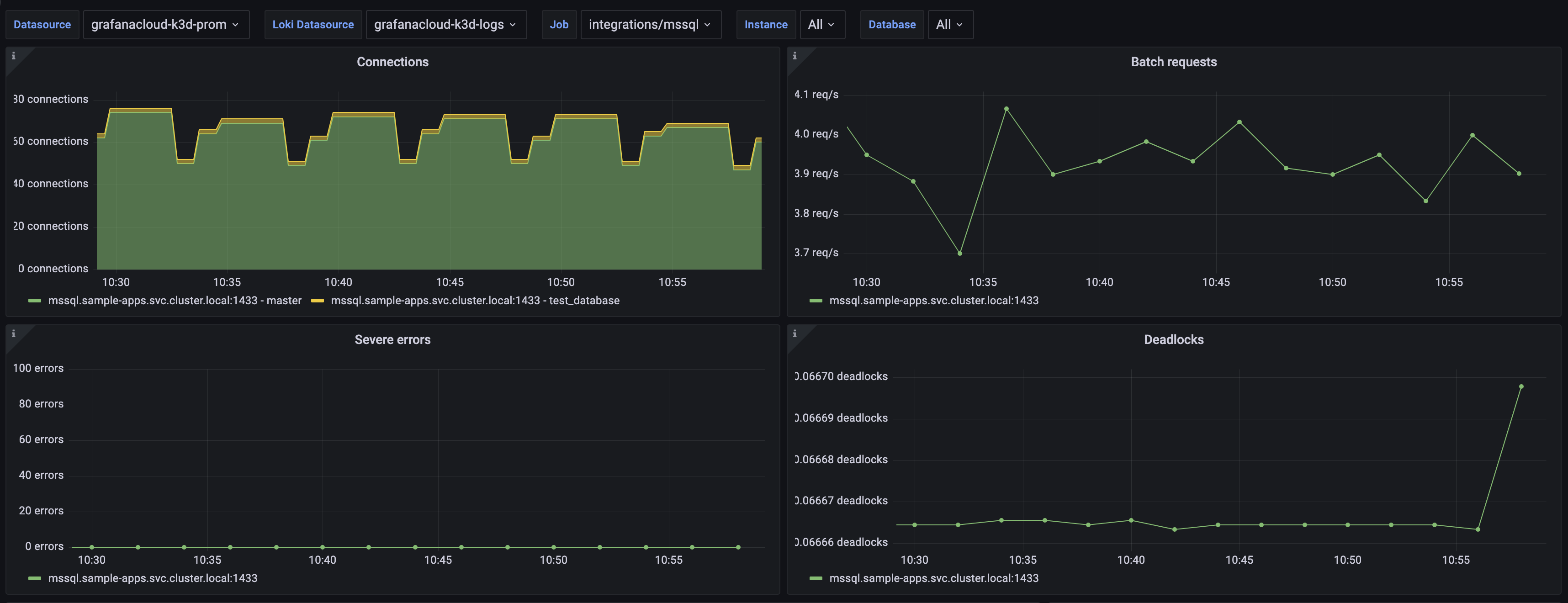
Microsoft SQL Server overview dashboard (2/3).

Microsoft SQL Server overview dashboard (3/3).
Alerts
The Microsoft SQL Server integration includes the following useful alerts:
Metrics
The most important metrics provided by the Microsoft SQL Server integration, which are used on the pre-built dashboards and Prometheus alerts, are as follows:
- mssql_available_commit_memory_bytes
- mssql_batch_requests_total
- mssql_buffer_cache_hit_ratio
- mssql_checkpoint_pages_sec
- mssql_connections
- mssql_deadlocks_total
- mssql_io_stall_seconds_total
- mssql_kill_connection_errors_total
- mssql_log_growths_total
- mssql_os_memory
- mssql_os_page_file
- mssql_page_fault_count_total
- mssql_server_target_memory_bytes
- mssql_server_total_memory_bytes
- up
Changelog
# 1.1.0 - March 2026
* Updated dashboards to follow new stylistic standards
# 1.0.5 - October 2024
* Pulled new mixin changes to apply a 1 minute `minstep` to any panels using `rate` or `increase`
# 1.0.4 - October 2024
* Pulled new mixin changes to use `$__rate_interval:` for all increase panels
# 1.0.3 - April 2024
* Added cluster selector to dashboards for kubernetes support
* Added default cluster label to agent config
* Bump version to 1.0.3
# 1.0.2 - March 2024
* Updates MSSQL integration with documentation for Windows authentication options
# 1.0.1 - December 2023
* Updates MSSQL integration with documentation for new query_config parameter
* Fixes prometheus metrics list to show new metrics added in 1.0.0
# 1.0.0 - December 2023
* Updates MSSQL integration to use newest MSSQL mixin
# 0.0.4 - September 2023
* Update Grafana Agent configuration snippets to include filtered metrics used in gauge panels
# 0.0.3 - September 2023
* New Filter Metrics option for configuring the Grafana Agent, which saves on metrics cost by dropping any metric not used by this integration. Beware that anything custom built using metrics that are not on the snippet will stop working.
* New hostname relabel option, which applies the instance name you write on the text box to the Grafana Agent configuration snippets, making it easier and less error prone to configure this mandatory label.
# 0.0.2 - August 2023
* Add regex filter for logs datasource
# 0.0.1 - February 2023
* Initial releaseCost
By connecting your Microsoft SQL Server instance to Grafana Cloud, you might incur charges. To view information on the number of active series that your Grafana Cloud account uses for metrics included in each Cloud tier, see Active series and dpm usage and Cloud tier pricing.


