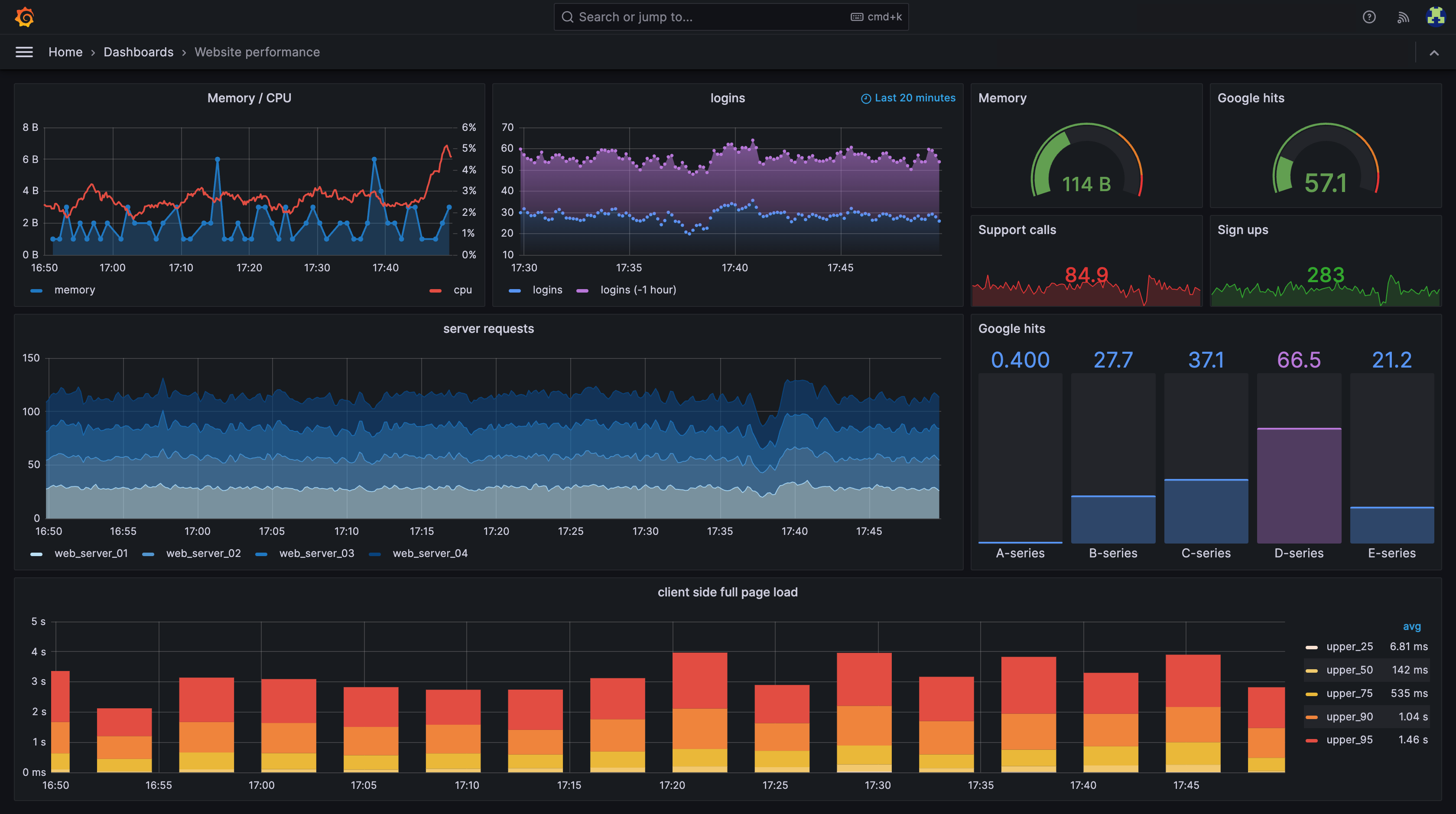
Visualize your data, optimize your performance
Easily collect, correlate, and visualize data with beautiful dashboards using Grafana — the open source data visualization and monitoring solution that drives informed decisions, enhances system performance, and streamlines troubleshooting.
The easiest way to get started with the latest version of Grafana is with Grafana Cloud, our fully managed observability stack.
Seamlessly build a single pane of glass
With 150+ Grafana plugins, you can unify all your data sources into a single dashboard to streamline data monitoring and troubleshooting.
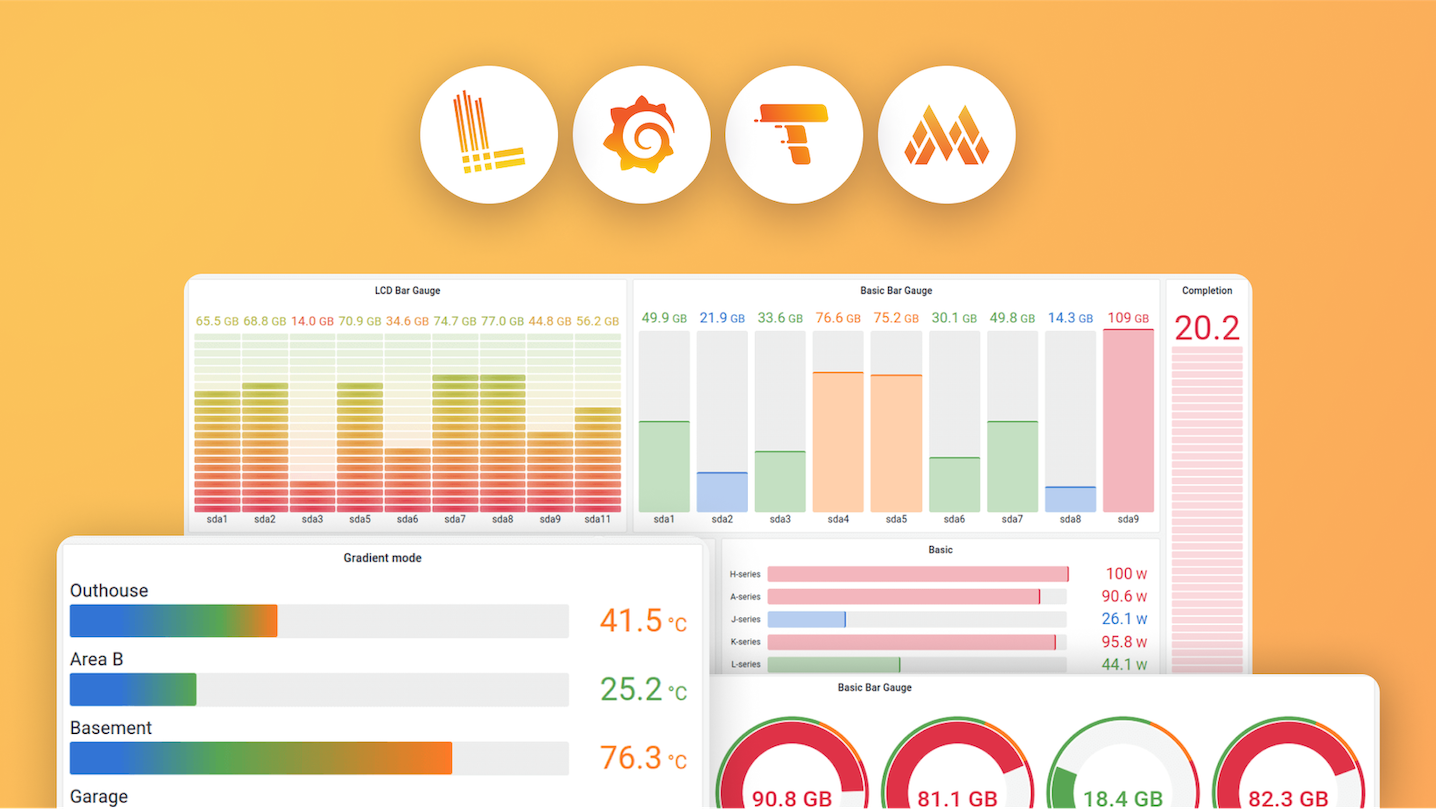
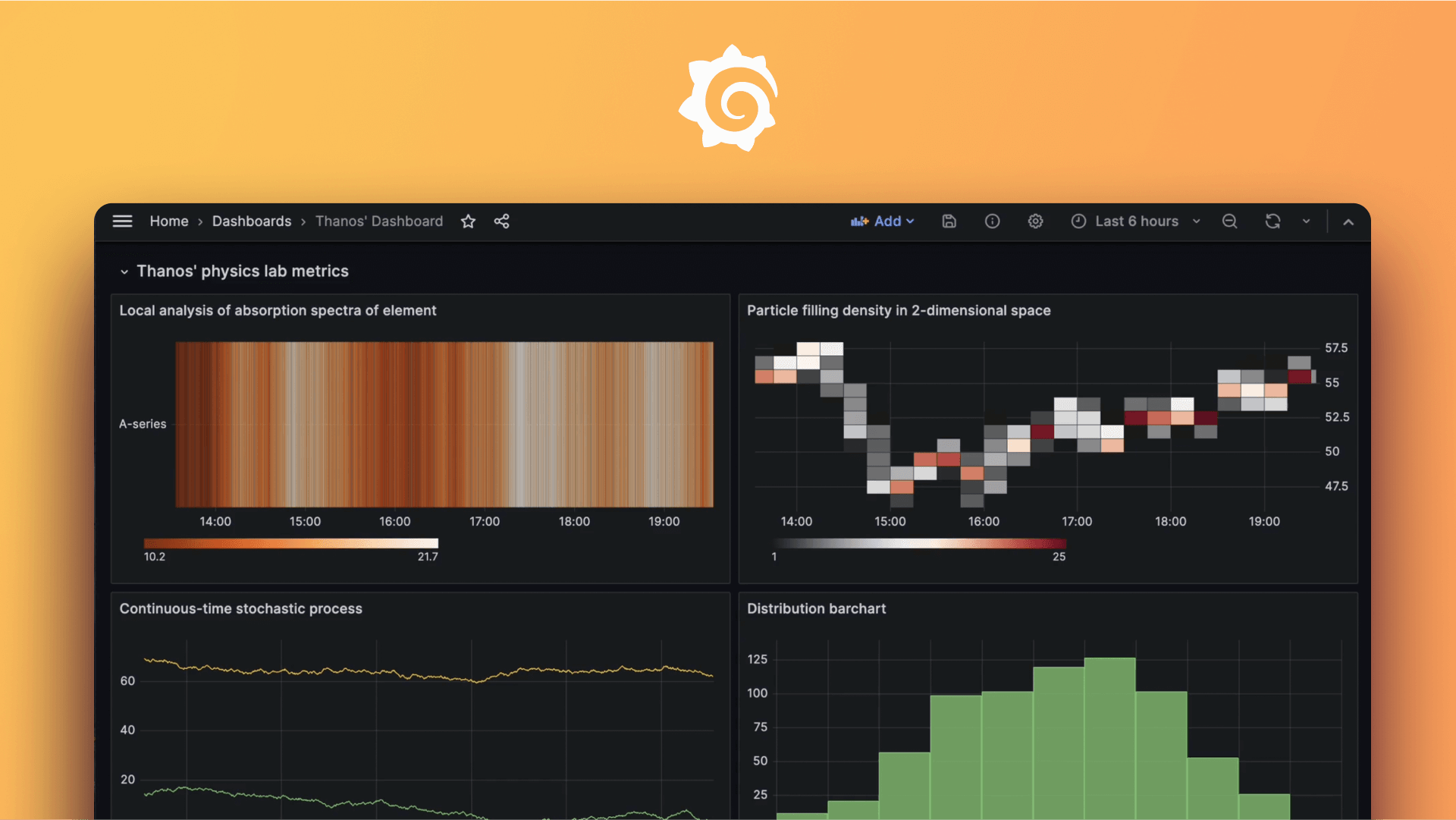
Transform data into real-time insights
Grafana’s growing suite of visualizations, ranging from time series graphs to heatmaps to cutting-edge 3D charts, help you decode complex datasets.
Manage observability as code
Deploy dashboards and alerts in your software pipeline, so that when a service ships, so does its monitoring.
The evolution of Grafana
- Explore and break down metrics by label without PromQL with Drilldown Metrics
- Scan, sort, and filter Loki logs with the new Logs table
- Nest folders into each other for cleaner organization and permissions
- Migrate directly from self-managed Grafana to Grafana Cloud
- Fine-tune Loki logs permissions with LBAC for the Loki data source
- Manage, store, and version your dashboards with Git Sync
- Organize dashboards with tabs or lay out and display panels responsively with dynamic dashboards
- Transform data in dashboards, alerting rules, or recording rules with SQL expressions
- Run cost-efficient queries on all data sources with Grafana-managed recording rules
- Dive into metrics, logs, traces and profiles without writing queries with Grafana Drilldown apps
- Go from zero to dashboards in minutes with dashboard templates and visualization suggestions
- Get access to our AI-powered agent with the Grafana Assistant plugin
- Set consistent standards and best practices for queries with saved queries
- Onboard and enable teams in product with interactive learning guides
- Perform regular health checks on your Grafana server with Grafana Advisor

Community-driven development is at the heart of Grafana
1.5M+
Active installs
67.5k
GitHub stars
2,000+
Contributors
25M+
Global users
Featured Grafana videos
Meet the Grafana contributors
Grafana Labs is proud to lead the development of the Grafana project. And we’re hiring!
Choose the version of Grafana that’s best for you
Get Grafana fully managed with Grafana Cloud or run on your own infrastructure with self-managed options.
Open source
Centralize the analysis, visualization, and alerting for all of your data with Grafana.
For users who prefer to set up, administer, and maintain their own installation.
Cloud
Offered as a fully managed service, Grafana Cloud is the fastest way to adopt Grafana and includes a scalable, managed backend for metrics, logs, and traces.
Managed and administered by Grafana Labs with free and paid options for individuals, teams, and large enterprises.
Includes a robust free tier with access to 10k metrics, 50GB logs, 50GB traces, 50GB profiles, 50k frontend sessions, and 500VUh of k6 testing for 3 users.
Enterprise
Grafana’s powerful visualization and alerting, enhanced with access to Enterprise data source plugins and built-in collaboration features.
For organizations that have specific privacy or security requirements and need a self-managed environment.