Security update: Grafana Labs does not believe it has been impacted by the Okta Lapsus$ breach
Status update on 2022-03-25 18:39:55 UTC: At this time, Grafana Labs has no reason to believe it has been impacted by the Okta Lapsus$ breach. This blog post has been updated.
On the morning of March 22 (UTC), news of a possible security breach of Okta by the Lapsus$ group started circulating on the internet. Okta has since confirmed that a breach did take place and that some customers were impacted. Okta is not used for customer authentication on our systems unless specifically configured as such by customers. We do not store any customer data in Okta. Okta is, however, used as Grafana’s primary Directory and Identity Provider internally.
Okta has provided confirmation confirming that Grafana was not impacted by the breach. We will continue to post any relevant updates here.
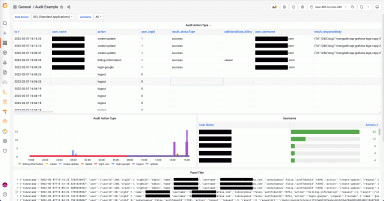
We have been reviewing our internal service logs for suspicious activity but have found nothing so far. This review has included correlating Okta user activity with event logs from external systems and services to identify any activity that may not have been captured by Okta’s logs. We have also taken this as an opportunity to focus additional effort to further improve our logging and forensic capabilities in this area.
Given some of the uncertainty still surrounding this incident, we are taking additional precautions such as expiring or rotating potentially at-risk sessions, credentials and authentication tokens, etc. We have also begun a review of our IdP systems and are evaluating options to improve the robustness of our internal authentication systems, reduce exposure to third-party service providers, and ensure that our security needs are adequately addressed.
If you have any questions or concerns, please contact our Support team by opening a ticket from within your grafana.com portal page.
Reporting security issues
If you think you have found a security vulnerability, please send a report to security@grafana.com. This address can be used for all of Grafana Labs’ open source and commercial products (including but not limited to Grafana, Grafana Cloud, Grafana Enterprise, and grafana.com). We can accept only vulnerability reports at this address. We would prefer that you encrypt your message to us by using our PGP key. The key fingerprint is
F988 7BEA 027A 049F AE8E 5CAA D125 8932 BE24 C5CA
The key is available from keyserver.ubuntu.com.
Security announcements
We maintain a security category on our blog, where we will always post a summary, remediation, and mitigation details for any patch containing security fixes.
You can also subscribe to our RSS feed.